
It has been a big year for realizing the limits of technology for interacting with people. Gamers have known this for a long time. Lag, disconnections, and coordination issues were problems in gaming since the start. There is a platform that has gone a long way in solving those problems: Discord.
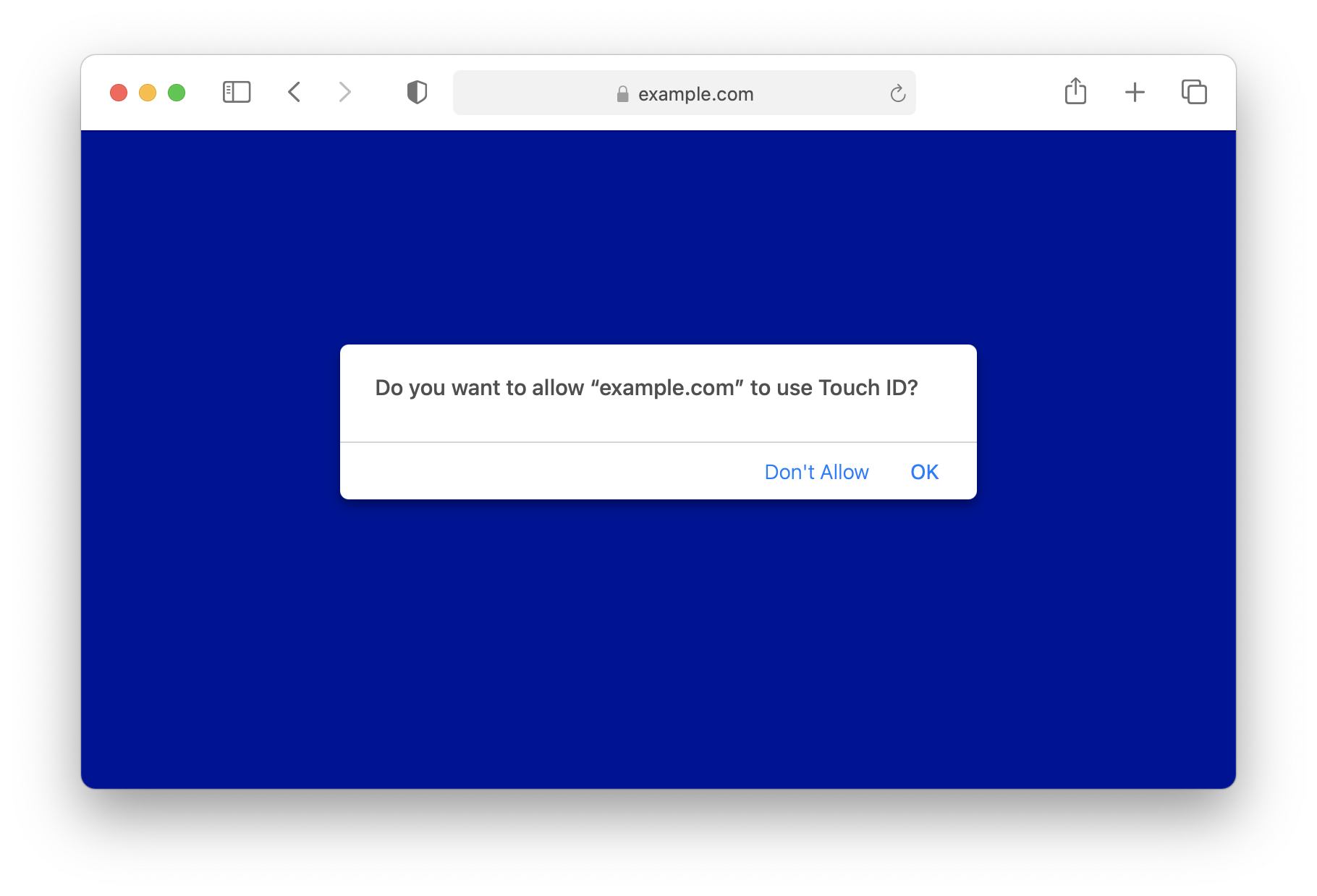
People often see passwords are the original sin of authentication on the web. Passwords can be easy to guess and vulnerable to breaches. Frequent reuse of the same password across the web makes breaches even more profitable.
You may have heard the terms “Architecture” or “System Design.” These come up a lot during developer job interviews – especially at big tech companies. This in-depth guide will help prepare you for the System Design interview, by teaching you basic software architecture concepts.
Updated Oct 27, 2016: Fixed sample code comments in coroutine example as per suggestion, edited text to note D’s similar behaviour. Updated Oct 28, 2016: Added missing colon., corrected Duff’s device example.

The most recent review left, regardless of its score, is weighted at 80%. This is why after a negative review is left, a company will routinely leave an onslaught of positive reviews to counterweight the negative one. Glassdoor is trash.

I’ve been reading about Eric Yuan, founder of Zoom. Yuan migrated to the USA from China in the 80s. He had heard Bill Gates speak about the internet and he wanted to be a part of the digital revolution.

“AI is the new electricity.” At least, that’s what Andrew Ng suggested at this year’s Amazon re:MARS conference.
Container security is a broad problem space and there are many low hanging fruits one can harvest to mitigate risks. A good starting point is to follow some rules when writing Dockerfiles. I’ve compiled a list of common security issues and how to avoid them.
![]()
We are pleased to announce HashiCorp Boundary, a new open source project that enables practitioners and operators to securely access dynamic hosts and services with fine-grained authorization without requiring direct network access.
In my job as a scientific software developer, I tend to write a lot of code. And most people who haven’t been through a Computer Science degree tend to think that CS is “just” about slinging code at the screen and then running it.

This issue stemmed from what I would qualify as an interrupted static HTML build. When building your Gatsby site the last steps of the build process involve building your production JS files and also generating the HTML for each page.
VPC is the topic that flies under the radar of many Software Developers, despite being present in every AWS account (well, maybe not for accounts created before 2009… But that’s unlikely). There are a few reasons for this I can think of:

Canny recently hit a major revenue milestone: one million dollars in annual recurring revenue. ⏱ We launched in March 2017, so it took us just under 3.
Thanks for your reading, save as your bookmark if you like my website.
